Multi-Factor Authentication (MFA) is a powerful and secure authentication method to force the users provide multiple security factors in order to prove their identities when they login to the system. One of these factors is something that the user knows, such as the username and password. The other factors are verification methods that they have, such as authentication app on a mobile device or a security key. It is a powerful way to increase the security of the users account and companies' data against cyberattacks.
If there is no Multi-Factor Authentication, anyone with the username and password can login to the system. However, since MFA requires at least two security factors, it makes it much harder for the bad actors to access your Salesforce environment. Even if bad actors know your username and password, they cannot login to the system unless you approve it with your second verification method (for example, an authenticator app).
You might be familiar with Two-Factor Authentication (2FA) and not with MFA. As you can understand from its name, MFA requires multiple verification methods, so it means that 2FA is also a type of MFA.
Requirement to Enable Multi-Factor Authentication
Starting from February 1, 2022, Salesforce will require all the users to use MFA in order to login to Salesforce. All the internal users that are logging in to Salesforce through the user interface must use MFA for every login. If there are users that are using SSO to login to Salesforce and your SSO system uses MFA, you don’t also need to enable Salesforce’s MFA for those users. It is possible to enable Multi-Factor Authentication for specific profiles or specific users.
If you are not sure whether your implementation meets MFA requirements, use MFA Requirement Checker. It will guide you through some questions to get your answer.
Customers that don't enable MFA until February 1, 2022 will be out of compliance with their contractual obligations. If you don't enable MFA for the internal users, Salesforce will automatically enable MFA for users who log in directly to Salesforce products. After some point, the option to disable MFA will be removed. It sounds like a big change, and it is, but pay an extra attention that you meet this requirement by February 1st.
MFA Requirements for User Types
Internal users are the users that have standard user licenses and can access Salesforce org's user interface. These users must use MFA when logging in through the user interface. At the other hand, external users are the users that can only access Experience sites, e-commerce sites, employee communities or help portals. These external users do not need to use MFA in order to log in to the system.
MFA Requirements for Login Types and Authentication Methods
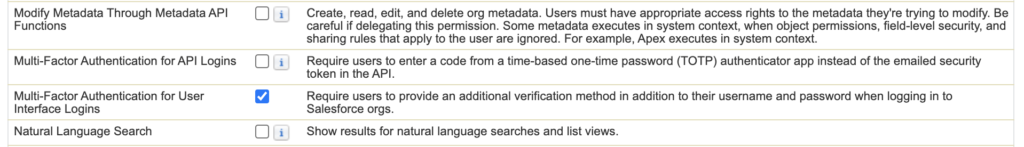
All the direct logins to the User Interface, including Salesforce interfaces, mobile apps and client apps like Data Loader, requires to use Multi-Factor Authentication. The most important question at this point is about the API/Integration logins. API and Integration logins don't need to use MFA. This rule is only for the users that are logging in to Salesforce through the UI whether by logging in directly or via SSO.
Enable MFA for Users
First of all, go to Session Settings in setup and add Multi-Factor Authentication as High Assurance in Session Security Levels.
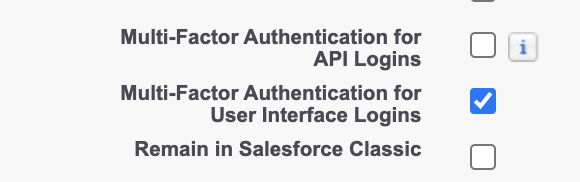
There are two ways to enable Multi-Factor Authentication for the users. First one is to enable it on the profile level and the second option is to create a permission set and assign it to the users.
In both of the options, you have to mark this checkbox under System Permissions.
Verification Methods for MFA
Verification Methods That Don't Satisfy the MFA Requirement
Sending one-time passwords via text messages, emails, or phone calls don't satisfy the Multi-Factor Authentication requirement. Moreover, security questions, trusted devices, trusted networks, or VPN do not satisfy the requirements.
Verification Methods That Satisfy the MFA Requirement
If you are using Single Sign On, you can use the MFA solution of your identity provider. If you are not using SSO, then you can use these supported methods:
- Salesforce Authenticator mobile app (Mobile app for iOS and Android)
- Time-based one-time passcode authenticator (TOTP) apps like Google Authenticator™ or Microsoft Authenticator™
- Physical security keys that support WebAuthn or U2F, such as Yubico’s YubiKey™ or Google’s Titan™ Security Key
- Built-in authenticators like Touch ID®, Face ID®, or Windows Hello™
Since it is Multi-Factor Authentication, you can register multiple verification methods. If you set up multiple verification methods, Salesforce uses this order:
- Salesforce Authenticator
- Built-in Authenticators
- Security Keys
- TOTP Authenticator Apps
Click here to read the Salesforce Multi-Factor Authentication FAQ article and learn more about MFA.
Salesforce Authenticator app is the most popular and most recommended MFA solution. Click here to learn more about this app and see the steps to configure it for your users.
You can read this post to learn more about the MFA enforcement roadmap.
MFA is extremely annoying and time consuming and forces me to have my phone with me at all times. I am at work and am unable to use my cell phone but thanks to you and this MFA i have to use my cell phoen everytime i log in which is propabley about 50 times a day. i need to know how to shut this off for certain users that use salesforce in the office only